- Loopback IP: x.x.x.x/32
- Public IP: 209.165.xy.x/24
- Private IP: 192.168.xy.x/24
- Tunnel IP: 169.254.xyz.x/24
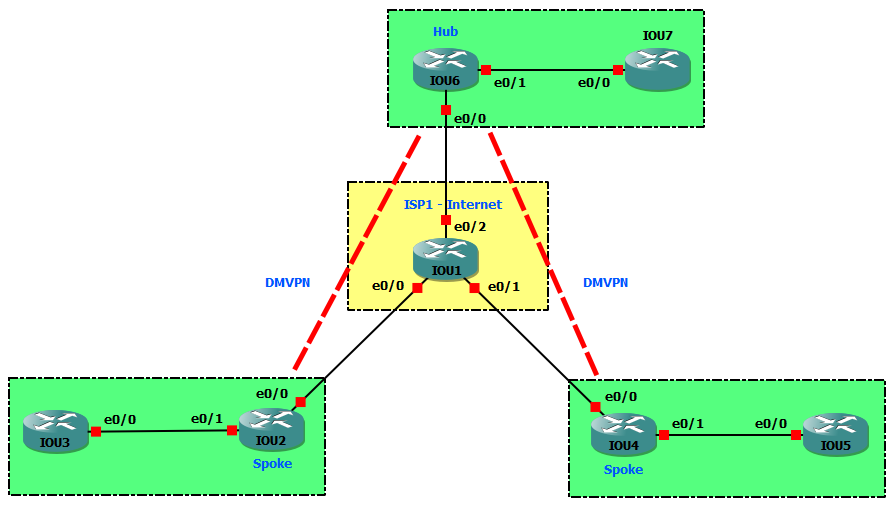
Task 1 Link to heading
- Configure EIGRP 1 on R1, R2, R4 and R6 to advertise Loopback 0 of R2, R4 and R6 to each other.
- Configure a static default route on R3 and R5 point to R2 and R4, respectively.
- Configure named EIGRP CCIE AS 100 in Hub and Spoke sites. Passive all inside LAN interfaces in Spoke sites.
Configuration Link to heading
hostname IOU1
int e0/0
ip add 209.165.12.1 255.255.255.0
no shut
int e0/1
ip add 209.165.14.1 255.255.255.0
no shut
int e0/2
ip add 209.165.16.1 255.255.255.0
no shut
router eigrp 1
no auto
net 0.0.0.0 255.255.255.255
hostname IOU2
int l0
ip add 2.2.2.2 255.255.255.255
int e0/0
ip add 209.165.12.2 255.255.255.0
no shut
int e0/1
ip add 192.168.23.2 255.255.255.0
no shut
router eigrp 1
no auto
net 2.2.2.2 0.0.0.0
net 209.165.12.0 0.0.0.255
router eigrp CCIE
address-family ipv4 autonomous-system 100
net 192.168.23.0 0.0.0.255
topology base
af-interface e0/1
passive-interface
hostname IOU3
int e0/0
ip add 192.168.23.3 255.255.255.0
no shut
ip route 0.0.0.0 0.0.0.0 192.168.23.2
hostname IOU4
int l0
ip add 4.4.4.4 255.255.255.255
int e0/0
ip add 209.165.14.4 255.255.255.0
no shut
int e0/1
ip add 192.168.45.4 255.255.255.0
no shut
router eigrp 1
no auto
net 4.4.4.4 0.0.0.0
net 209.165.14.0 0.0.0.255
router eigrp CCIE
address-family ipv4 autonomous-system 100
net 192.168.45.0 0.0.0.255
topology base
af-interface e0/1
passive-interface
hostname IOU5
int e0/0
ip add 192.168.45.5 255.255.255.0
no shut
ip route 0.0.0.0 0.0.0.0 192.168.45.4
hostname IOU6
int l0
ip add 6.6.6.6 255.255.255.255
int e0/0
ip add 209.165.16.6 255.255.255.0
no shut
int e0/1
ip add 192.168.67.6 255.255.255.0
no shut
router eigrp 1
no auto
net 6.6.6.6 0.0.0.0
net 209.165.16.0 0.0.0.255
router eigrp CCIE
address-family ipv4 autonomous-system 100
net 192.168.67.0 0.0.0.255
topology base
Verification Link to heading
IOU6#show ip route eigrp
2.0.0.0/32 is subnetted, 1 subnets
D 2.2.2.2 [90/435200] via 209.165.16.1, 00:00:23, Ethernet0/0
4.0.0.0/32 is subnetted, 1 subnets
D 4.4.4.4 [90/435200] via 209.165.16.1, 00:00:23, Ethernet0/0
D 209.165.12.0/24 [90/307200] via 209.165.16.1, 00:00:23, Ethernet0/0
D 209.165.14.0/24 [90/307200] via 209.165.16.1, 00:00:23, Ethernet0/0
IOU6#show ip eigrp nei
EIGRP-IPv4 Neighbors for AS(1)
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 209.165.16.1 Et0/0 10 00:00:37 16 100 0 12
EIGRP-IPv4 VR(CCIE) Address-Family Neighbors for AS(100)
H Address Interface Hold Uptime SRTT RTO Q Seq
(sec) (ms) Cnt Num
0 192.168.67.7 Et0/1 11 00:00:27 1 3000 0 1
Task 2: Link to heading
Configure DMVPN tunnels between R6, R2 and R4 as follows:
- Source tunnels from Loopback0 addresses.
- Use an NHRP network ID of 1.
- Use an NHRP authentication string of NHRPAUTH.
- Use GRE tunnel key of 2.
- DMVPN allows multicast.
- Enable EIGRP CCIE AS 100 on the tunnels.
- Ensure that Spokes send packets directly to each other.
Answer:
- By default, DMVPN allows only unicast => enable multicast by mapping to the NBMA address of Hub.
- Disable split-horizon on Hub to allow Spokes learn routes of each other.
- Using the command
no ip next-hop-self eigrp 100to not modify the next-hop value of EIGRP routes on Hub => allow Spokes send packets directly to each other.
Configuration Link to heading
IOU2(config)#
int tunnel 0
ip add 169.254.246.2 255.255.255.0
tunnel source l0
tunnel mode gre multipoint
ip nhrp nhs 169.254.246.6
ip nhrp map 169.254.246.6 6.6.6.6
ip nhrp map multicast 6.6.6.6
ip nhrp map multicast dynamic
ip nhrp network-id 1
ip nhrp authentication NHRPAUTH
tunnel key 2
router eigrp CCIE
address-family ipv4 autonomous-system 100
net 169.254.246.0 0.0.0.255
IOU4(config)#
int tunnel 0
ip add 169.254.246.4 255.255.255.0
tunnel source l0
tunnel mode gre multipoint
ip nhrp nhs 169.254.246.6
ip nhrp map 169.254.246.6 6.6.6.6
ip nhrp map multicast 6.6.6.6
ip nhrp map multicast dynamic
ip nhrp network-id 1
ip nhrp authentication NHRPAUTH
tunnel key 2
router eigrp CCIE
address-family ipv4 autonomous-system 100
net 169.254.246.0 0.0.0.255
IOU6(config)#
int tunnel 0
ip add 169.254.246.6 255.255.255.0
tunnel source l0
tunnel mode gre multipoint
ip nhrp map multicast dynamic
ip nhrp network-id 1
ip nhrp authentication NHRPAUTH
tunnel key 2
router eigrp CCIE
address-family ipv4 autonomous-system 100
net 169.254.246.0 0.0.0.255
af-interface Tunnel0
no next-hop-self
no split-horizon
Verification Link to heading
IOU2#show ip route eigrp
4.0.0.0/32 is subnetted, 1 subnets
D 4.4.4.4 [90/435200] via 209.165.12.1, 00:05:05, Ethernet0/0
6.0.0.0/32 is subnetted, 1 subnets
D 6.6.6.6 [90/435200] via 209.165.12.1, 00:04:50, Ethernet0/0
D 192.168.45.0/24 [90/102912000] via 169.254.246.4, 00:00:17, Tunnel0
D 192.168.67.0/24 [90/77312000] via 169.254.246.6, 00:00:17, Tunnel0
D 209.165.14.0/24 [90/307200] via 209.165.12.1, 00:05:26, Ethernet0/0
D 209.165.16.0/24 [90/307200] via 209.165.12.1, 00:05:26, Ethernet0/0
Task 3 Link to heading
No EIGRP, configure OSPF to form neighbor between Hub and Spokes via tunnels.
Answer:
By default, when OSPF is enabled, the network type of tunnel interface is point-to-point.
=> Change it to point-to-multipoint or broadcast, if not the OPSF will be flapping.
=> Broadcast is more preferable than point-to-multipoint. Because OSPF does not support next-hop-self command, with broadcast, the next hop will be redirected to other Spokes instead of Hub.
IOU6#show ip ospf int tun 0
Tunnel0 is up, line protocol is up
Internet Address 169.254.246.6/24, Area 0, Attached via Interface Enable
Process ID 100, Router ID 1.1.1.1, Network Type POINT_TO_POINT, Cost: 1000
Topology-MTID Cost Disabled Shutdown Topology Name
0 1000 no no Base
Enabled by interface config, including secondary ip addresses
Transmit Delay is 1 sec, State DOWN
Timer intervals configured, Hello 10, Dead 40, Wait 40, Retransmit 5
oob-resync timeout 40
Configuration Link to heading
IOU2(config)#
no router eigrp CCIE
router ospf 100
passive-interface e0/1
int e0/1
ip ospf 100 area 0
int tunnel 0
ip ospf 100 area 0
ip ospf network broadcast
ip ospf priority 0
IOU4(config)#
no router eigrp CCIE
router ospf 100
passive-interface e0/1
int e0/1
ip ospf 100 area 0
int tunnel 0
ip ospf 100 area 0
ip ospf network broadcast
ip ospf priority 0
IOU6(config)#
no router eigrp CCIE
router ospf 100
passive-interface e0/1
int e0/1
ip ospf 100 area 0
int tunnel 0
ip ospf 100 area 0
ip ospf network broadcast
Verification Link to heading
IOU2#show ip route ospf
O 192.168.45.0/24 [110/1010] via 169.254.246.4, 00:01:23, Tunnel0
O 192.168.67.0/24 [110/1010] via 169.254.246.6, 00:01:23, Tunnel0
IOU2#show ip ospf nei
Neighbor ID Pri State Dead Time Address Interface
6.6.6.6 1 FULL/DR 00:00:36 169.254.246.6 Tunnel0
Task 4 Link to heading
Configure IPsec tunnels as follows:
- Use an ISAKMP Policy with the following options:
- Pre-Shared Key: CISCO
- Encryption: 3DES
- Hash: MD5
- Diffie-Hellman Group: 5
- Use a Crypto Map named GRE_OVER_IPSEC_MAP with the following options:
- Loopbacks will be the tunnel endpoints
- GRE Traffic should be sent inside the IPsec tunnels
- Encrypt the traffic using 128-bit AES
- Authenticate the traffic using SHA-1
- Use ESP Transport mode to save additional encapsulation overhead
- To prevent the tunnel endpoints from having to do IPsec fragmentation, configure the GRE tunnel IP MTU to 1400 bytes, and set them to adjust the TCP MSS accordingly.
Answer:
- Loopbacks will be the tunnel endpoints =>
crypto map GRE_OVER_IPSEC_MAP local-address Loopback0 - Traffic goes from LAN sites to LAN sites is (IP over GRE) over IPSec
=> GRE header is combination of 2.2.2.2, 4.4.4.4 or 6.6.6.6.
=> Access-list for IPSec must match these GRE header, otherwise the IPSec tunnel cannot form.
- Enable
crypto map GRE_OVER_IPSEC_MAPon physical interfaces.
Configuration Link to heading
IOU2(config)#
crypto isakmp policy 10
encr 3des
hash md5
authentication pre-share
group 5
crypto isakmp key CISCO address 0.0.0.0
crypto ipsec transform-set ESP_AES_128_SHA_1 esp-aes 128 esp-sha-hmac
mode transport
crypto map GRE_OVER_IPSEC_MAP local-address Loopback0
ip access-list extended GRE_TRAFFIC
permit gre host 2.2.2.2 host 6.6.6.6
permit gre host 2.2.2.2 host 4.4.4.4
crypto map GRE_OVER_IPSEC_MAP 10 ipsec-isakmp
set peer 4.4.4.4
set peer 6.6.6.6
set transform-set ESP_AES_128_SHA_1
match address GRE_TRAFFIC
int tunnel 0
ip mtu 1400
ip tcp adjust-mss 1360
int e0/0
crypto map GRE_OVER_IPSEC_MAP
IOU4(config)#
crypto isakmp policy 10
encr 3des
hash md5
authentication pre-share
group 5
crypto isakmp key CISCO address 0.0.0.0
crypto ipsec transform-set ESP_AES_128_SHA_1 esp-aes 128 esp-sha-hmac
mode transport
crypto map GRE_OVER_IPSEC_MAP local-address Loopback0
ip access-list extended GRE_TRAFFIC
permit gre host 4.4.4.4 host 6.6.6.6
permit gre host 4.4.4.4 host 2.2.2.2
crypto map GRE_OVER_IPSEC_MAP 10 ipsec-isakmp
set peer 2.2.2.2
set peer 6.6.6.6
set transform-set ESP_AES_128_SHA_1
match address GRE_TRAFFIC
int tunnel 0
ip mtu 1400
ip tcp adjust-mss 1360
int e0/0
crypto map GRE_OVER_IPSEC_MAP
IOU6(config)#
crypto isakmp policy 10
encr 3des
hash md5
authentication pre-share
group 5
crypto isakmp key CISCO address 0.0.0.0
crypto ipsec transform-set ESP_AES_128_SHA_1 esp-aes 128 esp-sha-hmac
mode transport
crypto map GRE_OVER_IPSEC_MAP local-address Loopback0
ip access-list extended GRE_TRAFFIC
permit gre host 6.6.6.6 host 2.2.2.2
permit gre host 6.6.6.6 host 4.4.4.4
crypto map GRE_OVER_IPSEC_MAP 10 ipsec-isakmp
set peer 4.4.4.4
set peer 2.2.2.2
set transform-set ESP_AES_128_SHA_1
match address GRE_TRAFFIC
int tunnel 0
ip mtu 1400
ip tcp adjust-mss 1360
int e0/0
crypto map GRE_OVER_IPSEC_MAP
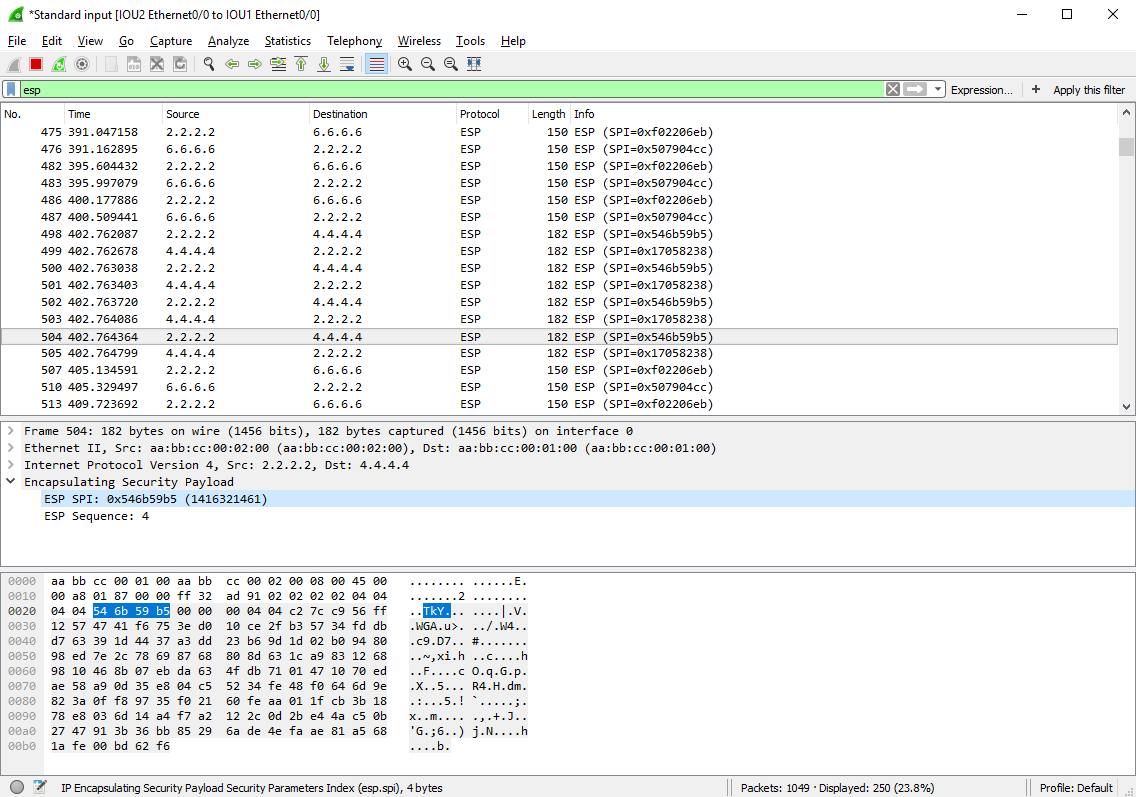
Verification Link to heading
IOU2#show crypto isakmp sa
IPv4 Crypto ISAKMP SA
dst src state conn-id status
4.4.4.4 2.2.2.2 QM_IDLE 1003 ACTIVE
6.6.6.6 2.2.2.2 QM_IDLE 1002 ACTIVE
IOU2#show crypto ipsec sa
interface: Ethernet0/0
Crypto map tag: GRE_OVER_IPSEC_MAP, local addr 2.2.2.2
protected vrf: (none)
local ident (addr/mask/prot/port): (2.2.2.2/255.255.255.255/47/0)
remote ident (addr/mask/prot/port): (4.4.4.4/255.255.255.255/47/0)
current_peer 4.4.4.4 port 500
PERMIT, flags={origin_is_acl,}
#pkts encaps: 4, #pkts encrypt: 4, #pkts digest: 4
#pkts decaps: 4, #pkts decrypt: 4, #pkts verify: 4
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 0, #recv errors 0
local crypto endpt.: 2.2.2.2, remote crypto endpt.: 4.4.4.4
path mtu 1500, ip mtu 1500, ip mtu idb Ethernet0/0
current outbound spi: 0x546B59B5(1416321461)
PFS (Y/N): N, DH group: none
inbound esp sas:
spi: 0x17058238(386236984)
transform: esp-aes esp-sha-hmac ,
in use settings ={Transport, }
conn id: 3, flow_id: SW:3, sibling_flags 80000000, crypto map: GRE_OVER_IPSEC_MAP
sa timing: remaining key lifetime (k/sec): (4365022/3363)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVE(ACTIVE)
inbound ah sas:
inbound pcp sas:
outbound esp sas:
spi: 0x546B59B5(1416321461)
transform: esp-aes esp-sha-hmac ,
in use settings ={Transport, }
conn id: 4, flow_id: SW:4, sibling_flags 80000000, crypto map: GRE_OVER_IPSEC_MAP
sa timing: remaining key lifetime (k/sec): (4365022/3363)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVE(ACTIVE)
outbound ah sas:
outbound pcp sas:
local crypto endpt.: 2.2.2.2, remote crypto endpt.: 6.6.6.6
path mtu 1500, ip mtu 1500, ip mtu idb Ethernet0/0
current outbound spi: 0x0(0)
PFS (Y/N): N, DH group: none
inbound esp sas:
inbound ah sas:
inbound pcp sas:
outbound esp sas:
outbound ah sas:
outbound pcp sas:
protected vrf: (none)
local ident (addr/mask/prot/port): (2.2.2.2/255.255.255.255/47/0)
remote ident (addr/mask/prot/port): (6.6.6.6/255.255.255.255/47/0)
current_peer 6.6.6.6 port 500
PERMIT, flags={origin_is_acl,}
#pkts encaps: 67, #pkts encrypt: 67, #pkts digest: 67
#pkts decaps: 67, #pkts decrypt: 67, #pkts verify: 67
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 0, #recv errors 0
local crypto endpt.: 2.2.2.2, remote crypto endpt.: 4.4.4.4
path mtu 1500, ip mtu 1500, ip mtu idb Ethernet0/0
current outbound spi: 0x0(0)
PFS (Y/N): N, DH group: none
inbound esp sas:
inbound ah sas:
inbound pcp sas:
outbound esp sas:
outbound ah sas:
outbound pcp sas:
local crypto endpt.: 2.2.2.2, remote crypto endpt.: 6.6.6.6
path mtu 1500, ip mtu 1500, ip mtu idb Ethernet0/0
current outbound spi: 0xF02206EB(4028761835)
PFS (Y/N): N, DH group: none
inbound esp sas:
spi: 0x507904CC(1350108364)
transform: esp-aes esp-sha-hmac ,
in use settings ={Transport, }
conn id: 1, flow_id: SW:1, sibling_flags 80000000, crypto map: GRE_OVER_IPSEC_MAP
sa timing: remaining key lifetime (k/sec): (4321374/3343)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVE(ACTIVE)
inbound ah sas:
inbound pcp sas:
outbound esp sas:
spi: 0xF02206EB(4028761835)
transform: esp-aes esp-sha-hmac ,
in use settings ={Transport, }
conn id: 2, flow_id: SW:2, sibling_flags 80000000, crypto map: GRE_OVER_IPSEC_MAP
sa timing: remaining key lifetime (k/sec): (4321374/3343)
IV size: 16 bytes
replay detection support: Y
Status: ACTIVE(ACTIVE)
outbound ah sas:
outbound pcp sas:
IOU3#ping 192.168.45.5
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.45.5, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/7/10 ms
Now all LAN traffic (include EIGRP hello) is encrypted as ESP packets:
Task 5 Link to heading
- Delete the above crypto map GRE_OVER_IPSEC_MAP.
- Use IPsec Profile named GRE_OVER_IPSEC_PROFILE with the same options.
Answer: Enable IPSec Profile on tunnel interface.
Configuration Link to heading
IOU2(config)#
int e0/0
no crypto map GRE_OVER_IPSEC_MAP
exit
no crypto map GRE_OVER_IPSEC_MAP
crypto ipsec profile GRE_OVER_IPSEC_PROFILE
set transform-set ESP_AES_128_SHA_1
int tunnel 0
tunnel protection ipsec profile GRE_OVER_IPSEC_PROFILE
IOU4(config)#
int e0/0
no crypto map GRE_OVER_IPSEC_MAP
exit
no crypto map GRE_OVER_IPSEC_MAP
crypto ipsec profile GRE_OVER_IPSEC_PROFILE
set transform-set ESP_AES_128_SHA_1
int tunnel 0
tunnel protection ipsec profile GRE_OVER_IPSEC_PROFILE
IOU6(config)#
int e0/0
no crypto map GRE_OVER_IPSEC_MAP
exit
no crypto map GRE_OVER_IPSEC_MAP
crypto ipsec profile GRE_OVER_IPSEC_PROFILE
set transform-set ESP_AES_128_SHA_1
int tunnel 0
tunnel protection ipsec profile GRE_OVER_IPSEC_PROFILE
Verification Link to heading
IOU3#ping 192.168.45.5
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.45.5, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 1/1/1 ms